A recent malware campaign distributed via phishing emails has targeted organizations worldwide in order to infect Windows user’s devices.
The trojan malware identified as Trojan.VB.Crypt is installed on the victim’s devices and was developed in Visual Basic 5.0. The author associated this threat is called Stiffveined0 and was identified in PE File properties. According to SI-LAB, its name is not related to other existed past threats.
This RAT has been disseminated via phishing campaigns, and the PE malicious file is named SWITF DOO, val EUR, Iznos 120410.38, Datum 26.11.2018.exe by its authors. The first released was noted on Nov 26, 2018, and the first submission onto VirusTotal was performed by SI Lab on 27 Nov 2018 with a classification rate of 24/69.

When malware is initiated, it executes a scan in the victim’s device in order to discover sensitive files. All the activities are performed without user’s knowledge, including capturing keyboard input, collecting system information, dropping other malware into the infected system, performing denial-of-service (DoS) attacks, and running/terminating processes.
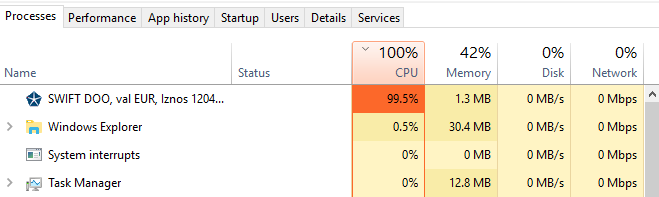
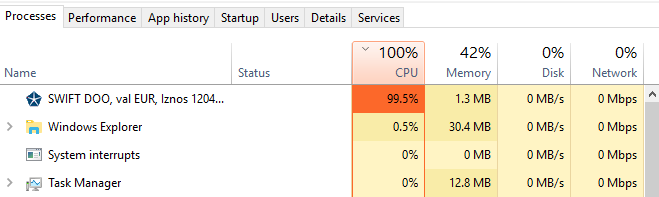
The CPU increases to 100% at the time of the first run and remains hidden for several seconds. Next, It keeps asleep in the operating system process tree.
During the infection, the RAT tries to be persistent by creating registry keys in the system and also copies itself in the system32 directory — an evidence was found during our analysis.
No activity related to C2 was detected and no more information is available at the moment.
New developments and findings will be shared.
— 29-11-2018
Another malware variant was detected.
File name: swift copy.exe and Rivkah.exe
MD5: 3a03b0da50c986f1f281615833a8e44b
SHA-1: 9a02debbfd533904ce16e38107fe5dcc17d99226
Imphash: dc3790a43ce30e7278fb33defdb0b4be
SSDeep: 12288:7X8XqJfii6tvoxiV8msk1W1HN5p7iaJoMmh4QJY:7saJ3YoiVt870Y
VirusTotal Report here.
[Last update: 29-11-2018]
Malware Analysis – Details
The malware initially distributed through a phishing campaign via organizational addresses has attacked many organizations. The email body was sent in the Bosnian language, as can be seen below:

Other emails in English were also sent by crooks:
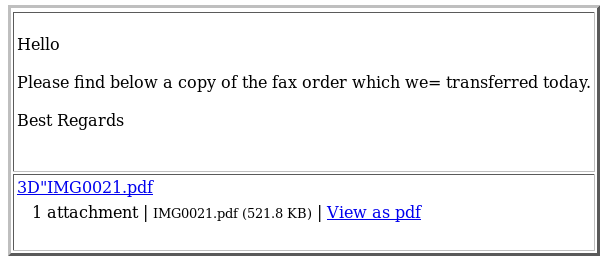
Both the emails and the malware were extracted via SMTP connections via a technique so-called file carving.
After getting the malware from the malicious connections, we looking for pieces of evidence or public hashes related this threat in VirusTotal but no results were found — we were facing a rising threat.
The first detection was observed on Mon, 26 Nov 2018 18:23:25 +0000 (UTC).
The malware came as an email attachment and called SWITF DOO, val EUR, Iznos 120410.38, Datum 26.11.2018.exe.
![]()
According to SI-LAB research, this malware was developed in Visual Basic 5.0; some tools even point to version 6.0. The PEiD points to the “Microsoft Visual Basic 5.0 / 6.0.

Some indicators point out that a crypter was used to protect the malware, VB.Crypter.Vir, but that not happened, as we can see below.
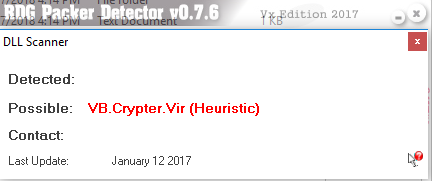
SI-LAB team was able to reach the p-code generated in Visual Basic 5.0 and used by criminals to make this threat possible. The unpacking code itself is written in VB 5.0 , which ends up as interpreted bytecode (p-code). The only way to figure out the unpacking algorithm is to reverse engineer this code. It’s possible to build VB apps as native code, but for whatever reason, many RunPE variants will only run if they’re built as p-code and not as native executables. This also makes it harder to reverse engineer… (There are now some versions that use VB.NET, which isn’t p-code or native, but .NET CIL).

The malware is composed by a Form with several timers in order to execute different timers with malicious behavior.
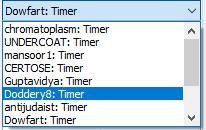
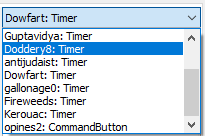
Crooks used 10 timers to execute malicious actions in a certain period of time.
When the malware starts the process, a machine scan for sensitive files and also accesses the system registry in order to gain persistence in the infected machine is executed. The processor spikes until 100% of execution rate, as can be seen in the following image.
The malware uses 6 functions listed in blacklists, and 12 blacklisted strings are also detected.

After its execution, anomalous behavior is identified. The malware creates a temporary file where information is stored in binary format. It was not possible to obtain the information in plain-text, nor to undesrstand what type of information is registered.
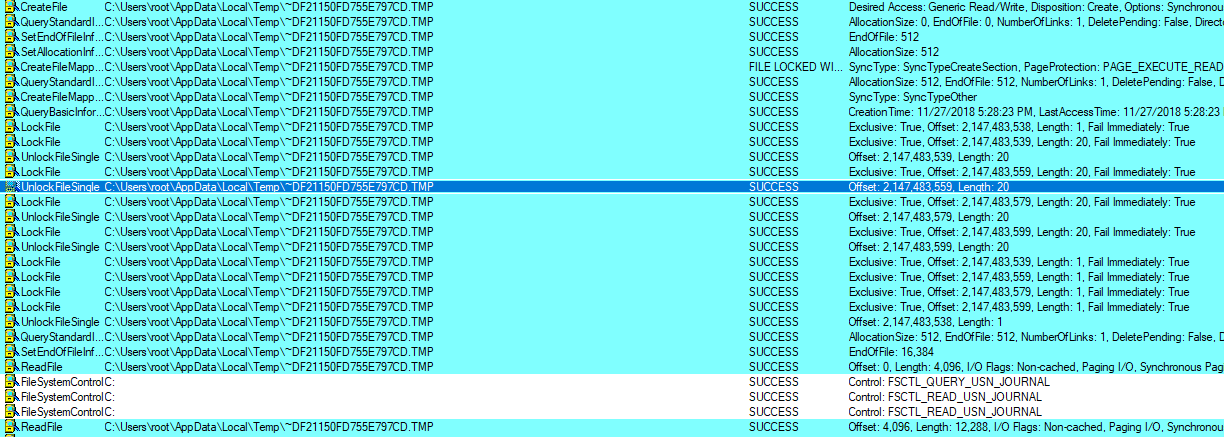
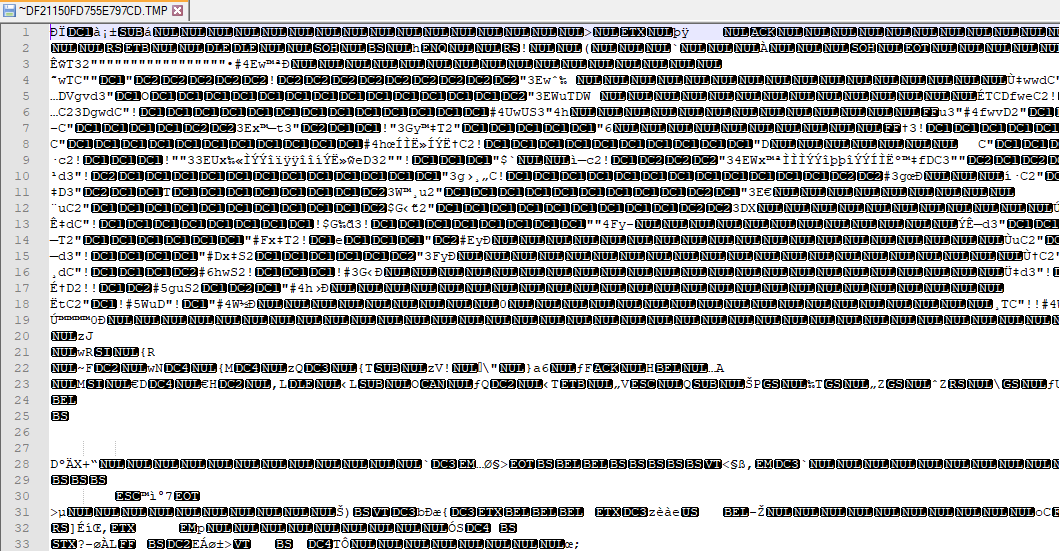
The purpose of the file could not be identified, but it is suspected that it is information about the device and that it is later used in another type of malicious behavior.
During the analysis, there were no C&C server IPs or other indicators related to the remote server. However, this malware has been registered as a trojan derived from its behavior.
Shortly after the creation of the temporary file, the malware creates a copy of itself.
![]()
At the end of the manual dynamic analysis performed by SI-LAB, the malware was first submitted to VirusTotal and obtained a rating of 24/60.
Indicators of Compromise

Filesize: 585.66 KB
MD5: 5BD1831AE0B42C86D6FE0EED571DE641
SHA1: 720ba91f587c492cfb54acd0f3f1f6c732ccd06b
Imphash: e39b953ababc114a863c53e3c9a8d610
SSDeep: 6144:EKgcPVzpyhiuCYC1L2NedvCr1Cl0euApsnt2mSo2Nba6MTOsSeFec/bPdejn:FD9zKkYCGedWcPS29sSeFVIj
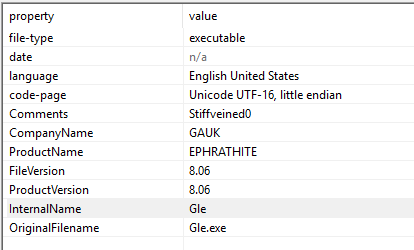
Property: Stiffveined0
Company: GAUK
Product Name: EPHRATHITE
File Version: 80.6
Internal Name: Gle
https://www.virustotal.com/#/file/33c9bc7a51adf43d84c16b70505519f30e63d8b9230d7a2a2bf7dcd84d733221
