This week a huge set of information on the Islamic state has been shared in a Dark Web forum.
The first occurrence of this share was registered in a tweet by @GhostSquadHack published on February 13th.

All data have been extracted from the victim’s mobile devices, including, satellite geo-location, target’s Telegram images folder (sdcard) and target’s WhatsApp images folder (sdcard). Phone numbers, documents, credit cards, identification cards/documents, Telegram, Facebook and Twitter accounts as well as IP logs were also exfiltrated by crooks.

As shown, data from several countries were found in this collection, including Indonesia, Morocco, Turkey, India, etc.
Many personal photographs, videos, SMS, phone numbers extracted from the hacked devices can be found by analyzing the data, as well as images and documents of the group’s internal publications.
Additional evidence is presented below.

(medicare card)
 (contact list sample)
(contact list sample)

(SMSs)

(Telegram account and details)
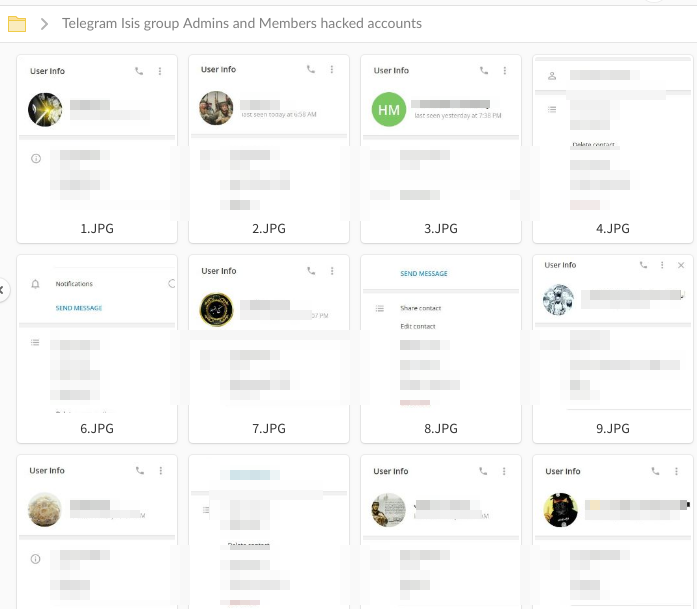
(Telegram account details 2)
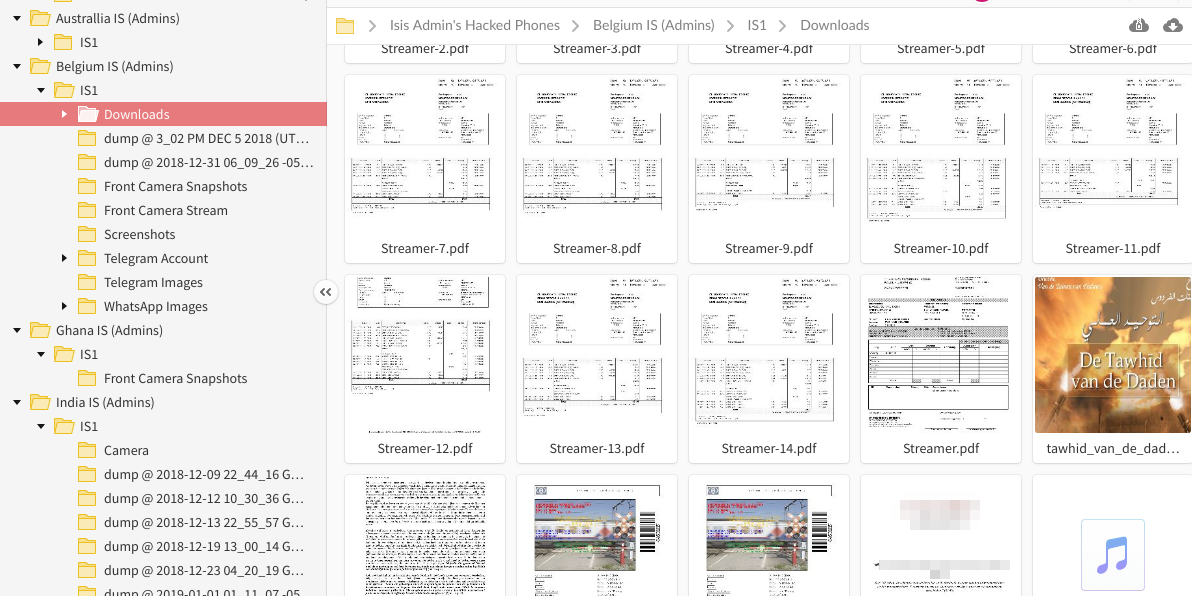
(other documents)
According to this share, Telegram and WhatsApp are the preferred communication channel used by members of the Islamic state.
The leak is now available for download and can be used for malicious purposes.
No more information is available at the moment.
