Another day and another AWS bucket with vital data is exposed publicly on the Internet – this time, the tech giant, GoDaddy.
Security researchers with the UpGuard Cyber Risk Team today disclosed that they found the giant in domain registration and hosting left an Amazon S3 bucket wide open for public consumption.
Data exposed includes documents that detailed configurations for tens of thousands of GoDaddy systems. Additionally, documents with pricing information about these systems were also exposed in the same S3 bucket.
“Essentially, this data mapped a very large scale AWS cloud infrastructure deployment, with 41 different columns on individual systems, as well as summarized and modeled data on totals, averages, and other calculated fields,” UpGuard’s researchers reported. “Also included were what appear to be GoDaddy’s discounts from Amazon AWS, usually restricted information for both parties, who must negotiate for rates.”
Many information was exposed online, including data about hostname, operating system, memory, CPU, AWS region, and what the specific workloads were being used for. This would be extremely valuable for attackers seeking to map out GoDaddy’s infrastructure to help direct future malicious activity and find particularly juicy targets.

“Similar ‘casing’ info is often sought through social engineering and internet-research to make other attacks as effective and efficient as possible,” UpGuard’s report notes. “The ‘workload’ column particularly would help point attackers in the right direction, highlighting which systems serve more important functions and likely house important data.”

The exposed pricing data could have been used to the competitive advantage of GoDaddy rivals, technology service vendors, and cloud providers.
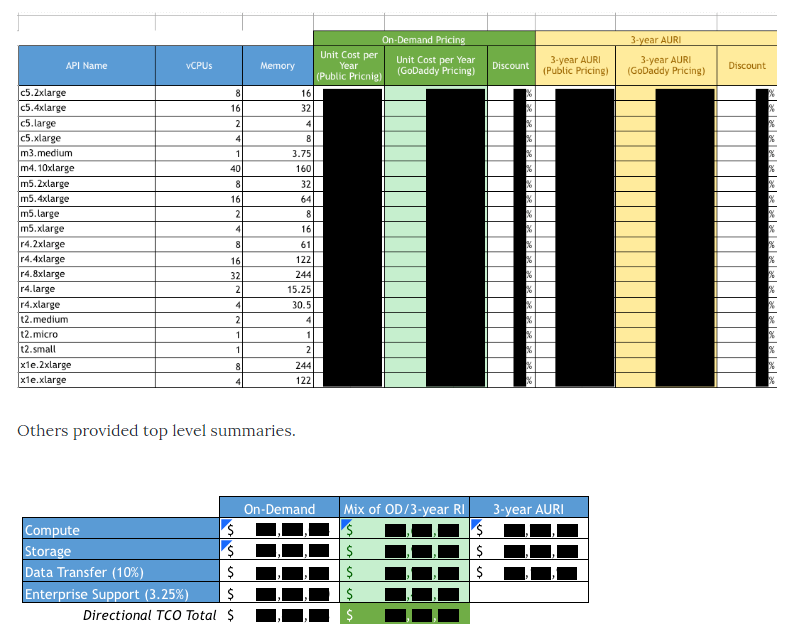
“Knowing the details of GoDaddy’s AWS discounts could give others a negotiation advantage and price point that would otherwise be unknown,” the report explains. “Furthermore, the way in which GoDaddy allocates their cloud spend is also strategic – this is a blueprint for running cloud infrastructure at the largest scales.”
Amazon S3 buckets are securely configured by default, nonetheless, GoDaddy is far from the only company to open up its cloud storage with very little authentication protections. This year alone, organizations including Accenture, FedEx, and Walmart were all similarly exposed.
According to one study earlier this year by Digital Shadows, researchers estimated that 1.5 billion sensitive files are visible on the Internet from misconfigured S3 buckets, NAS devices, FTP servers, and other cloud storage systems.
Enjoy the report here.
